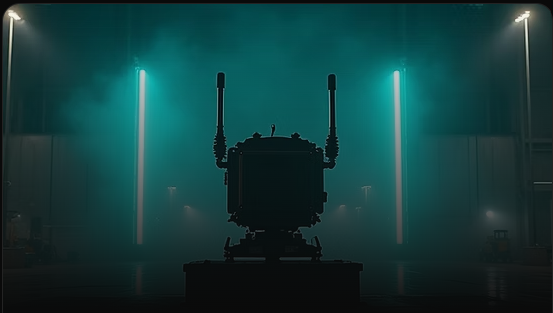
Fixed UAV monitoring system enabling remote detection, identification, and networked airspace surveillance with all-weather reliability.

Fixed unmanned aerial vehicle (UAV) monitoring system designed for remote detection and identification of drones. It supports large-scale model recognition, networked deployment, blacklist/whitelist management, and reliable all-weather operation for continuous airspace monitoring.
System Capabilities
Advanced technological features defining the JDY-RID superiority in the field.
Continuously monitors common UAV communication bands to detect and identify drones within the coverage area.
Accurately identifies 300+ UAV models and decodes Remote ID data including drone ID, position, altitude, and trajectory.
Detects and tracks multiple drones at the same time, maintaining stable performance in complex airspace environments.
Supports multi-unit networking to extend coverage, eliminate blind zones, and enable centralized monitoring.
Enables controlled identification of authorized and unauthorized drones for precise monitoring and decision-making.
IP66-rated design ensures reliable performance in harsh weather and demanding environmental conditions.
A streamlined defense protocol designed for rapid response and maximum effectiveness
Detailed operational parameters for mission planning and system integration.
Decodes drone Remote ID data including identity, position, altitude, and flight trajectory.
Recognizes and classifies 300+ commercial UAV models for rapid threat attribution.
Tracks multiple drones simultaneously with stable performance in congested airspace.
Supports multi-unit networking for expanded coverage and centralized monitoring control.
Separates authorized drones from unknown or hostile targets using list-based management.
Rugged IP66-rated housing ensures dependable all-weather operation for fixed deployment.
System Capabilities
The system continuously scans and monitors the surrounding RF spectrum to detect UAV communication links and Remote ID broadcast signals in real time, ensuring early detection of drones operating within or approaching the protected monitoring zone.
Once a drone signal is detected, the system captures and decodes Remote ID broadcast data including drone identity, serial information, real-time position, altitude, speed, and flight path telemetry for detailed situational awareness.
Captured data is analyzed using internal UAV recognition databases to identify drone model, manufacturer, and operational characteristics, allowing operators to quickly determine whether the drone is authorized, unknown, or potentially hostile.
The system continuously tracks detected drones and displays real-time location, trajectory, altitude, and movement patterns through the monitoring interface, enabling operators to maintain full airspace visibility across the coverage area.
If an unauthorized or suspicious drone is detected, the system automatically generates alerts, logs flight activity, and continues persistent monitoring to support security teams with actionable data for further response or investigation.
Proven protection across critical sectors and high-security environments
Secures power plants, refineries, ports, data centers, and industrial facilities by detecting and disrupting unauthorized drones before they pose safety, espionage, or sabotage risks.

Supports frontline units and patrol teams with portable UAV detection and countermeasures, enabling rapid response against hostile or reconnaissance drones in asymmetric combat environments.

Enhances border posts, checkpoints, and restricted zones by identifying low-altitude drone intrusions used for smuggling, surveillance, or unauthorized crossings.

Provides temporary airspace protection for high-profile events, government gatherings, and VIP movements through fast deployment and real-time drone threat neutralization.

Assists police and rapid response teams in controlling rogue drones during investigations, protests, disaster zones, or emergency operations without relying on fixed infrastructure.
Built for the rigorous demands of modern defense and critical infrastructure protection.
Accurately decodes and analyzes UAV Remote ID broadcasts, providing real-time drone identity, position, and flight telemetry.
Supports identification of 300+ commercial drone models, enabling faster classification and response decisions.
Simultaneously monitors multiple UAVs, maintaining stable performance in complex or high-traffic airspace environments.
Supports multi-unit deployment for extended coverage and centralized airspace monitoring control.
Enables separation of authorized drones from unknown or suspicious UAV activity for controlled monitoring.
IP66-rated design ensures reliable performance in outdoor and harsh environmental conditions.
Designed for professional defense, government, and authorized security personnel.
Suitable for fixed, mobile, and temporary deployments worldwide.
Seamlessly integrates with existing C2 systems and security infrastructure.
This counter-drone defense system is a controlled technology designed for authorized security and defense applications only. Deployment requires proper licensing, regulatory approval, and trained personnel. Unauthorized use, sale, or export is strictly prohibited and may result in severe legal consequences. All operators must comply with local, national, and international laws governing radio frequency interference and airspace security.
Request a demonstration, download technical specifications, or speak with our defense systems specialists to learn how our counter-drone technology can protect your critical infrastructure.
Access detailed specifications, deployment guides, and compliance documentation
Schedule a secure demonstration at your facility or our testing grounds
Speak with our defense specialists about custom deployment solutions